I'm Pushpender Singh Rathore
Cybersecurity Analyst
I'm Pushpender, a second-year B.Tech CSE student at BRCM CET. I build advanced tools, explore cybersecurity, and write code in C/C++, Assembly, and Python. I enjoy problem-solving by breaking systems in isolated lab environments (legally). Experienced in malware and botnet analysis with tools like Ghidra, gdb, YARA, xxd, objdump, and Binary Ninja, and in machine learning using Transformers, PyTorch, TensorFlow, NumPy, Ollama, scikit-learn, Pandas, and the high-level Keras API. I build efficient daemons and explore IoT and system-level concepts that support offensive security research and ethical hacking.


Experience
About Me
I'm a cybersecurity practitioner based in India with a strong foundation in security research and machine learning. I've been seriously focused on offensive security for the past couple of years and I'm constantly learning and adapting to new technologies. Currently pursuing a B.Tech in Computer Science (2nd year) at BRCM CET, Bahal.
I specialize in analysing responsive botnets, researching Advanced Persistent Threats (APTs) and state-sponsored malware, working with neural networks, and developing on cloud-based VPS infrastructure using modern frameworks and libraries. My approach combines technical depth with creative problem-solving - thinking outside the box on exploitation, studying zero-day vulnerabilities in controlled environments, and prioritising ethical research practices.
When I'm not coding, you can find me exploring new technologies, contributing to open-source projects, and sharing knowledge with the cybersecurity community through my blog and social media.
Education
B.Tech Computer Science Engineering
RSCIT Computer Diploma
Location
Gogameri, Rajasthan (currently Bahal, Haryana)
Experience
2+ years in the cybersecurity domain
Skills & Expertise
Programming
Cyber & Networking
Web & Tools
Operating Systems
Certifications
OSCP – Offensive Security Certified Professional
Hands-on penetration testing certification covering enumeration, exploitation, privilege escalation, and Active Directory attacks.
Verification link coming soonCEH – Certified Ethical Hacker
EC-Council certification covering reconnaissance, scanning, system hacking, malware threats, and web application attacks.
Verification link coming soonCompTIA Security+
Foundational security certification covering threats, attacks, cryptography, identity management, and risk mitigation.
Verification link coming soonRSCIT Computer Diploma
Basic computer fundamentals, digital literacy, and IT systems knowledge.
Verification link coming soonWhat I Do
Low-level Programming
Writing efficient programs in C/C++ and exploring system internals.
Security Practice
CTF practice, vulnerability exploration, and learning pentesting Advanced.
Reverse Engineering & Automation
APK projects, Malware Autopsy , and Neural Networks to automate tasks.
Featured Projects
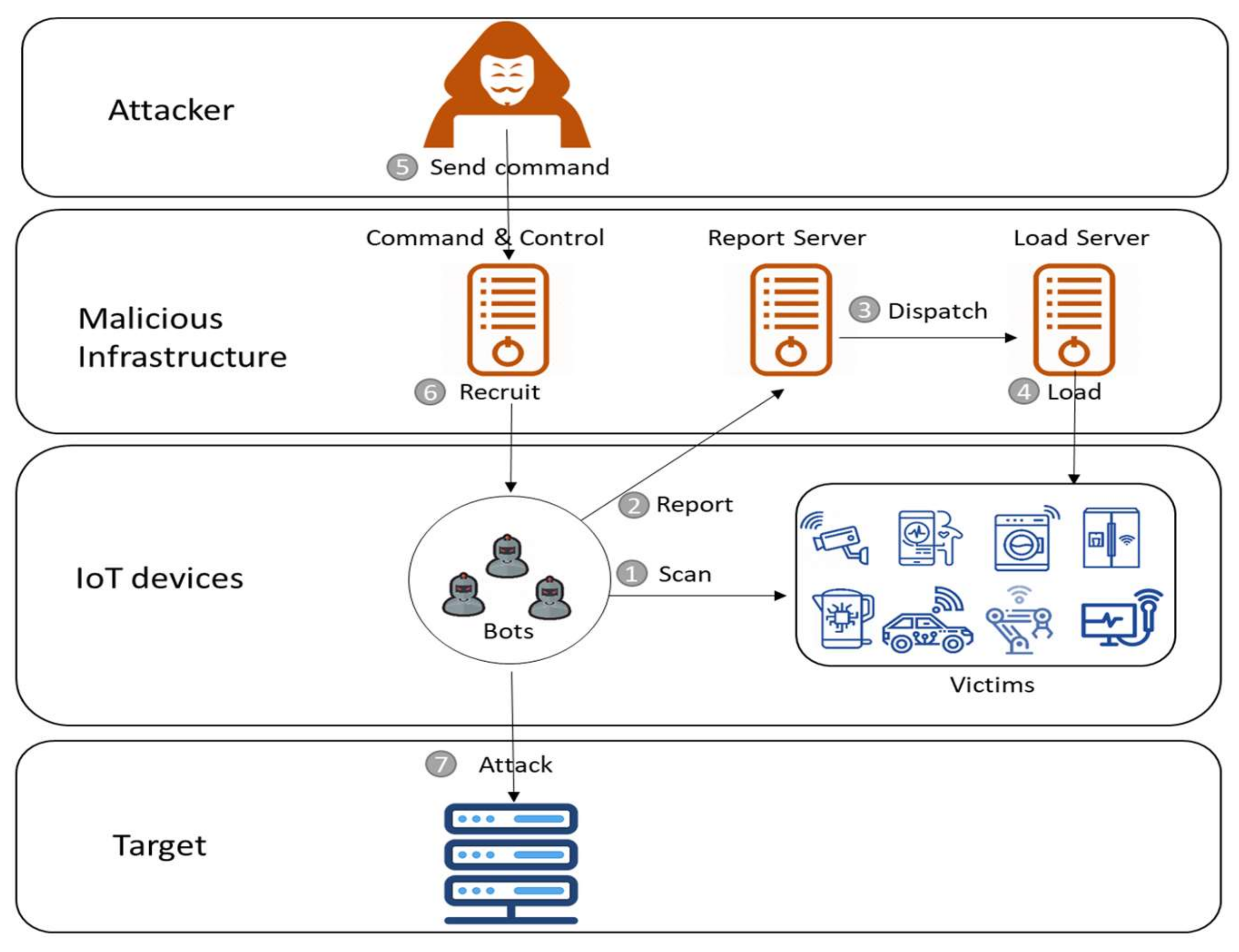
Mirai Source Code
This repository contains the Mirai botnet source code preserved strictly for educational, research, and cybersecurity analysis purposes. It is intended to help learners and security professionals understand how large-scale IoT malware operates at a technical level.
Open Source Intelligence
The repository includes resources for network reconnaissance, domain and IP intelligence, email and username enumeration, social media intelligence (SOCINT), geolocation analysis (GEOINT), and metadata extraction. All tools and workflows focus on ethical OSINT practices and legal intelligence gathering.

Contactsd - Encrypted Contacts Daemon
Contactsd is a secure CLI-based contacts management system built using modern cryptography. It encrypts all stored data using AES-256-GCM, providing confidentiality, integrity, and authentication. Encryption keys are derived from a master password using PBKDF2-HMAC-SHA256 with 150,000 iterations and a unique salt for each record. All cryptographic operations are implemented via OpenSSL. Without the correct master password, stored data remains unreadable and tamper-detection is enforced through GCM authentication tags.

Mac Address Randomizer
A privacy-focused systemd-based Linux service that periodically randomizes MAC addresses for all active network interfaces using macchanger. The service supports Arch, Debian, and Fedora-based distributions, utilizes dynamic interface detection, and includes a kill-switch to block network access if MAC spoofing fails, ensuring consistent privacy protection.

Blackarch opensource contribution
This repository focuses on working with BlackArch-Linux, a penetration-testing and security-research distribution built on Arch Linux. It is designed for learning and practicing ethical hacking, cybersecurity analysis, and offensive security techniques in a controlled and legal environment.

Venice-firewall
The system integrates both offline AI models and online AI services to analyze network traffic patterns, detect suspicious or anomalous behavior, and automatically resolve traffic decisions without manual intervention with Admin Mail Messaging System. This enables real-time adaptive filtering and intelligent security enforcement.